Was sind die Data Spaces?
Data Spaces sind dezentralisierte Ökosysteme, die den vertrauenswürdigen Datenaustausch erleichtern sollen. In einem Data Space interagieren verschiedene Parteien – Datenanbieter, Verbraucher und Vermittler – innerhalb eines Rahmens, der Sicherheit, Datenschutz und Compliance gewährleistet. Dieser Austausch findet in der Regel zwischen digitalen Geldbörsen statt, die von Identitätsanbietern verwaltet werden, und wird von Konnektoren unterstützt, die die sichere Übertragung von Daten übernehmen.
Ein Data Space ermöglicht es Einzelpersonen oder Organisationen (Datenanbietern), ihre Daten mit anderen (Datenkonsumenten) zu teilen und gleichzeitig die Kontrolle darüber zu behalten, wer darauf zugreift und unter welchen Bedingungen. Diese Umgebungen sind so konzipiert, dass sie die Datenhoheit respektieren, d. h. sicherstellen, dass die Daten innerhalb eines bestimmten rechtlichen und regulatorischen Rahmens bleiben, und die Privatsphäre der Nutzer schützen. Data Spaces fördern das Vertrauen, die Transparenz und die Sicherheit, so dass es für Unternehmen einfacher wird, wertvolle Informationen auszutauschen und gleichzeitig die Risiken im Zusammenhang mit Datenschutzverletzungen zu verringern.
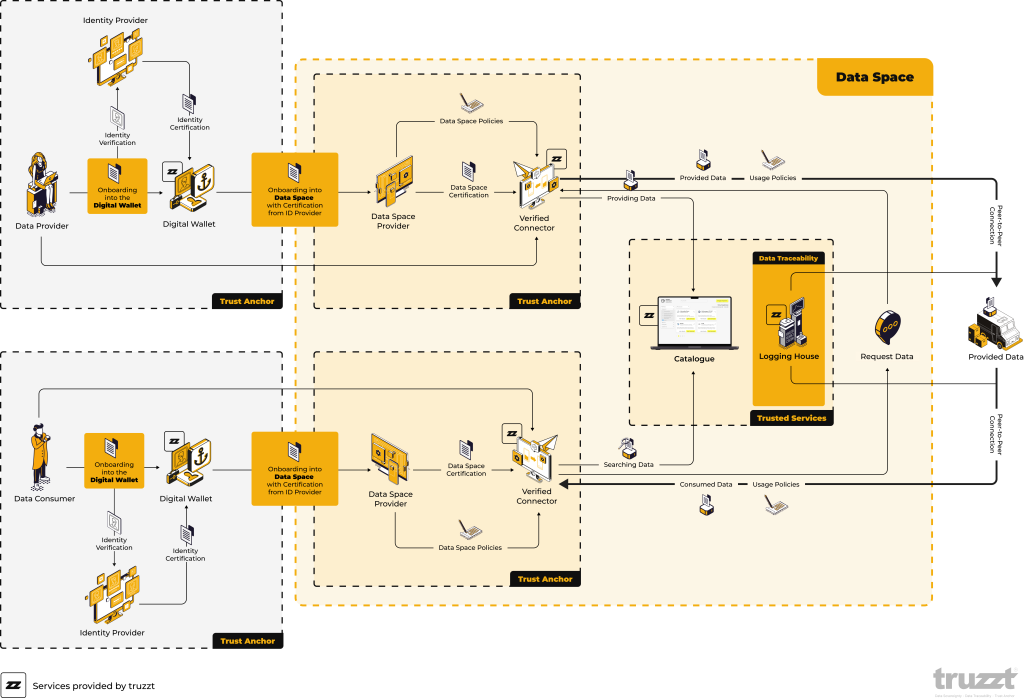
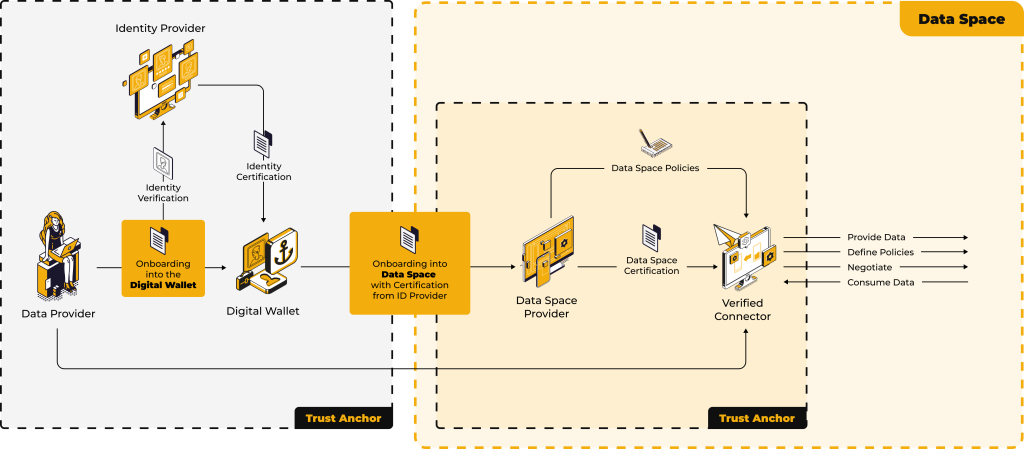
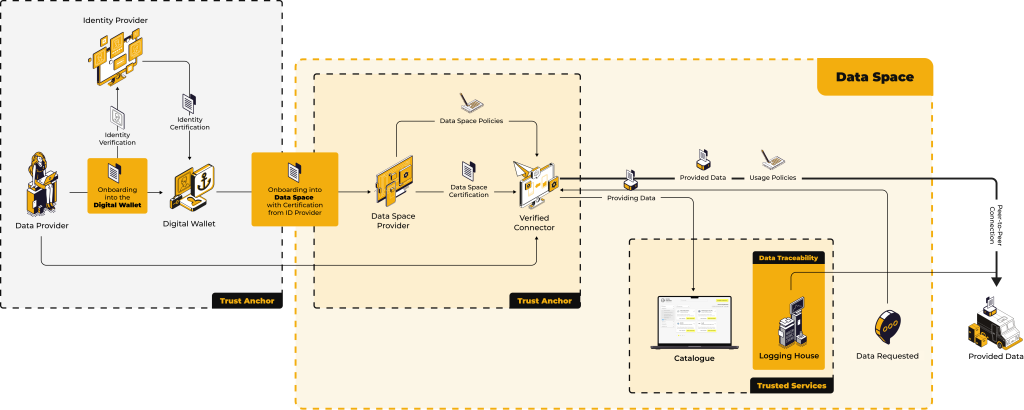
Der Onboarding-Prozess
Identitätsüberprüfung und digitale Geldbörsen
Der Einführungsprozess in einen Data Space beginnt mit der Identitätsprüfung. Nutzer (entweder Datenanbieter oder Verbraucher) müssen ihre Identitätsdaten an einen Identitätsanbieter übermitteln. Der Identitätsanbieter prüft die Anmeldedaten des Nutzers und stellt ein Zertifikat aus, das die Identität des Nutzers bestätigt. Dieses Zertifikat wird in einer digitalen Brieftasche gespeichert, die als sicherer Speicherplatz für die verifizierte Identität des Nutzers dient.
Der Konnektor wird dann für den Zugriff auf den Data Space verwendet. Diese Software oder dieses Tool ist für die Interaktion mit dem Datenraum, die Vertretung des Nutzers innerhalb des Ökosystems und die sichere Abwicklung des Datenaustauschs zuständig.
Wer stellt die digitale Brieftasche zur Verfügung?
Die digitale Brieftasche wird von vertrauenswürdigen Anbietern bereitgestellt und verwaltet. Dabei kann es sich um spezialisierte Unternehmen oder Organisationen handeln, die Erfahrung mit der Verwaltung sensibler Daten haben. Die Wallet-Anbieter sind für die Sicherheit der gespeicherten Anmeldedaten verantwortlich und stellen sicher, dass nur befugte Personen auf sie zugreifen können. In einigen Fällen kann eine Wallet auch in die Data-Spaceplattform selbst integriert sein, was den Prozess für die Nutzer vereinfacht.
Gemeinsame Nutzung und Verbrauch von Daten
Datenanbieter
Ein Datenanbieter ist eine Person oder Organisation, die wertvolle Daten zur Verfügung stellt. Durch die Teilnahme an einem Datenraum können Datenanbieter ihre Daten hochladen und katalogisieren und sie vertrauenswürdigen Datenkonsumenten zur Verfügung stellen. Es gibt zwei Gründe, warum Datenanbieter an einem Datenraum teilnehmen sollten:
Sicherheit
Datenräume stellen sicher, dass die Daten des Anbieters nur autorisierten Verbrauchern zugänglich sind und schützen sie vor unbefugtem Zugriff oder Verstößen.
Monetarisierung
Anbieter können Nutzungsbedingungen festlegen, die auch Preise für den Datenverbrauch beinhalten können, und so neue Einnahmequellen schaffen. Eine vertrauenswürdige Umgebung wie ein Datenraum reduziert die Reibungsverluste beim Abschluss von Vereinbarungen mit Verbrauchern und gewährleistet, dass alle Transaktionen nachvollziehbar sind und den Datenschutzgesetzen entsprechen.
Datenverbraucher
Datenkonsumenten hingegen suchen nach spezifischen Daten, die ihre Arbeit verbessern können. Sie können nach Daten suchen und diese bei den Anbietern in diesem Bereich anfordern. Der Konnektor des Verbrauchers stellt sicher, dass seine Anfrage ordnungsgemäß überprüft wird und mit den Bedingungen des Anbieters übereinstimmt, bevor die Daten freigegeben werden.
Die Verbraucher profitieren von der Transparenz des Datenraums, da sie sicher sein können, dass die Daten, die sie erhalten, überprüft und vertrauenswürdig sind und von seriösen Anbietern stammen.
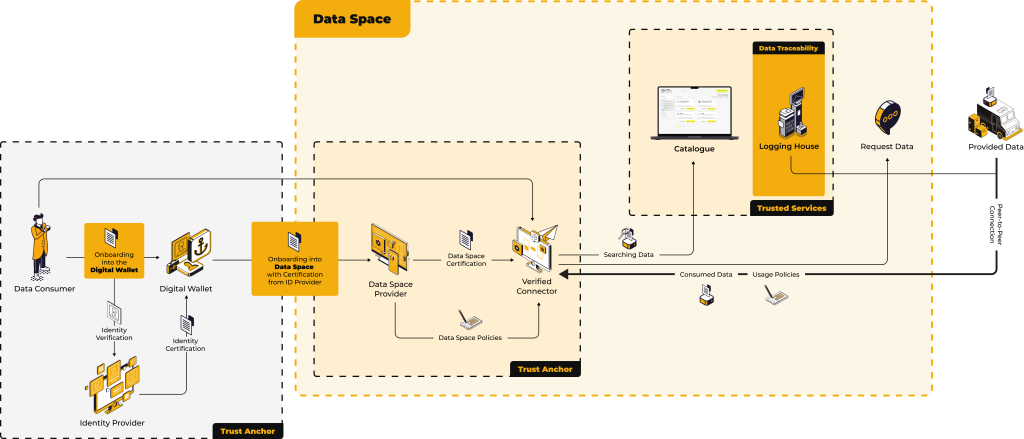
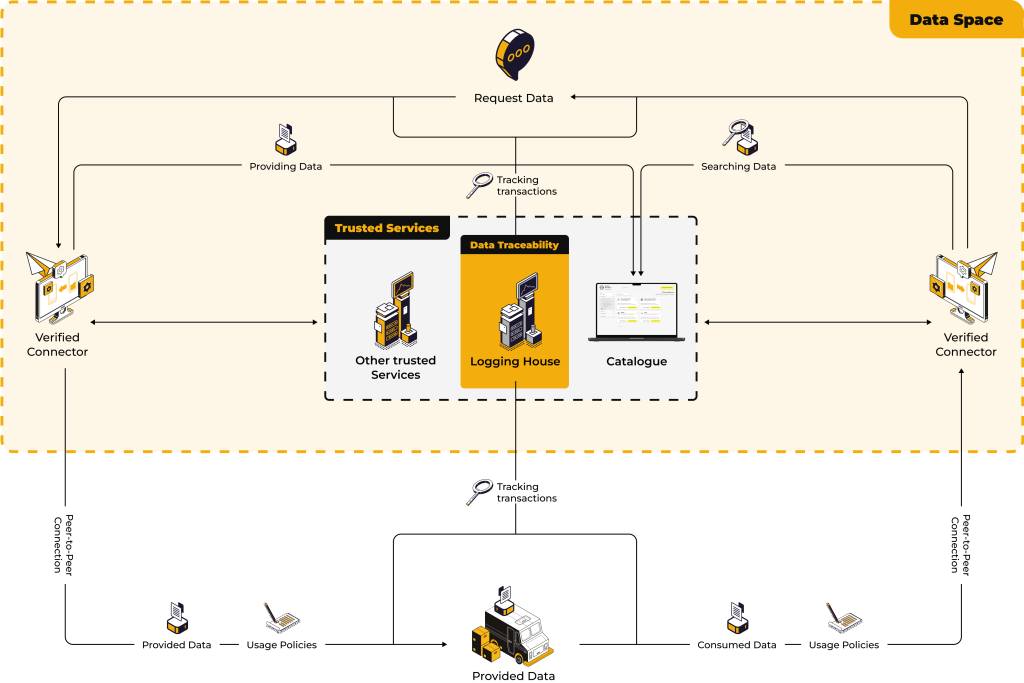
Sicherstellung von Vertrauen und Rückverfolgbarkeit
Eine der wichtigsten Komponenten eines Datenraums ist das Logging House. Während der Datenaustausch zwischen den beiden Konnektoren stattfindet, zeichnet das Logging House jede Transaktion auf, um die Rückverfolgbarkeit zu gewährleisten. Das bedeutet, dass, obwohl die Daten selbst direkt zwischen den Konnektoren (außerhalb des Datenraums selbst) übertragen werden, das Logging House einen sicheren Prüfpfad aufrechterhält.
Datenverbraucher
Die Transaktion findet direkt zwischen den beiden Konnektoren statt, ohne dass ein Dritter im Datenraum zwischengeschaltet ist. Dadurch wird sichergestellt, dass keine unnötige Datenweiterleitung oder -speicherung erfolgt und das Risiko von Datenlecks minimiert wird. Die Konnektoren fungieren als vertrauenswürdige Agenten sowohl für den Datenanbieter als auch für den -verbraucher und wickeln den Datenaustausch sicher ab, während die Protokollierungsstelle sicherstellt, dass jede Aktion für zukünftige Referenzen und die Einhaltung von Vorschriften nachverfolgt wird.